SERVICES
User Experience Research
User Interface Design
Design System
Framer Development
3D Design
CATEGORY
SAAS
B2B
LINKS
TECH STACK
DURATION
4 Months
CHALLENGES
- Crafting a serious, professional, and trustworthy brand presence for a cybersecurity firm working with both public institutions and corporations.
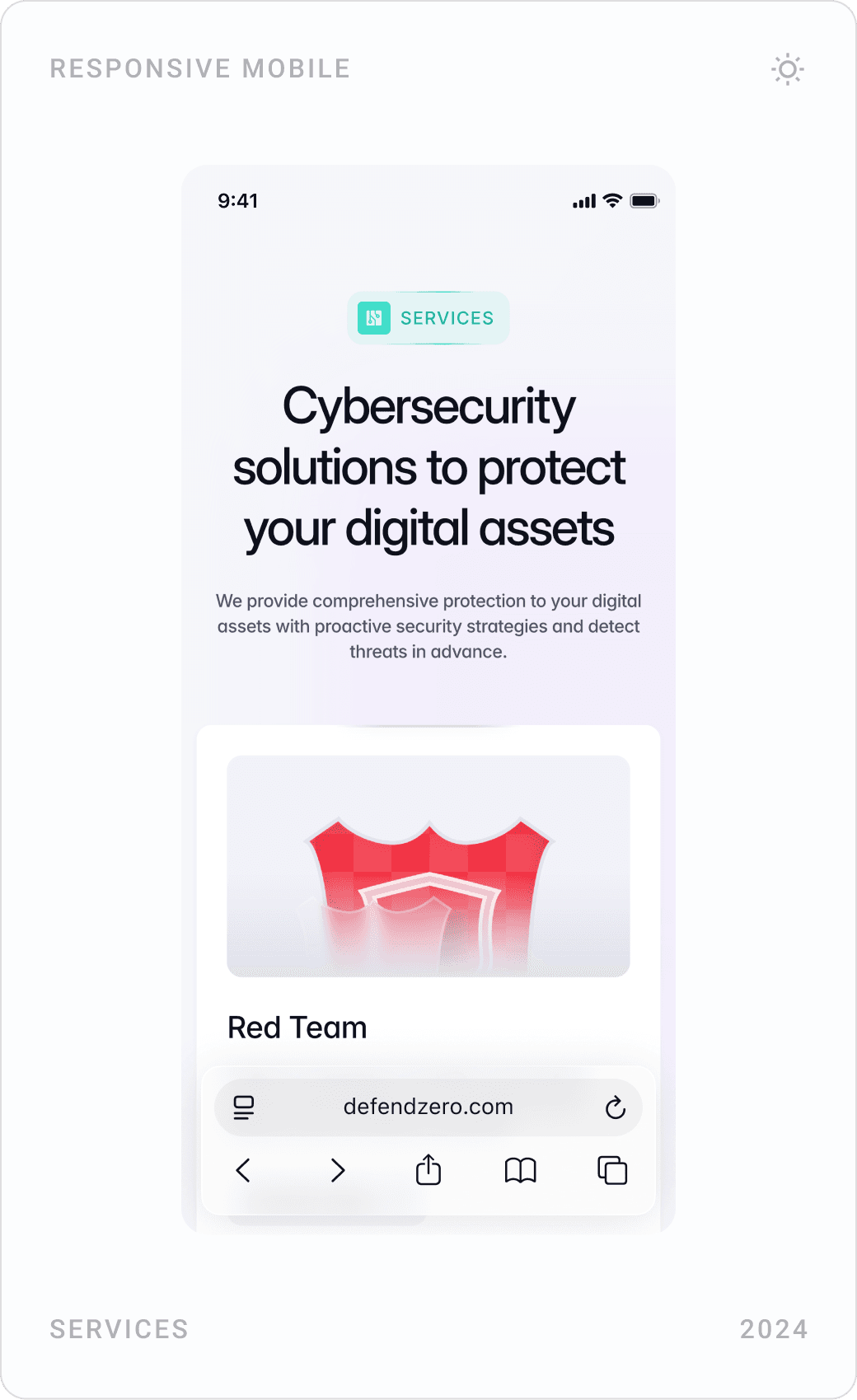
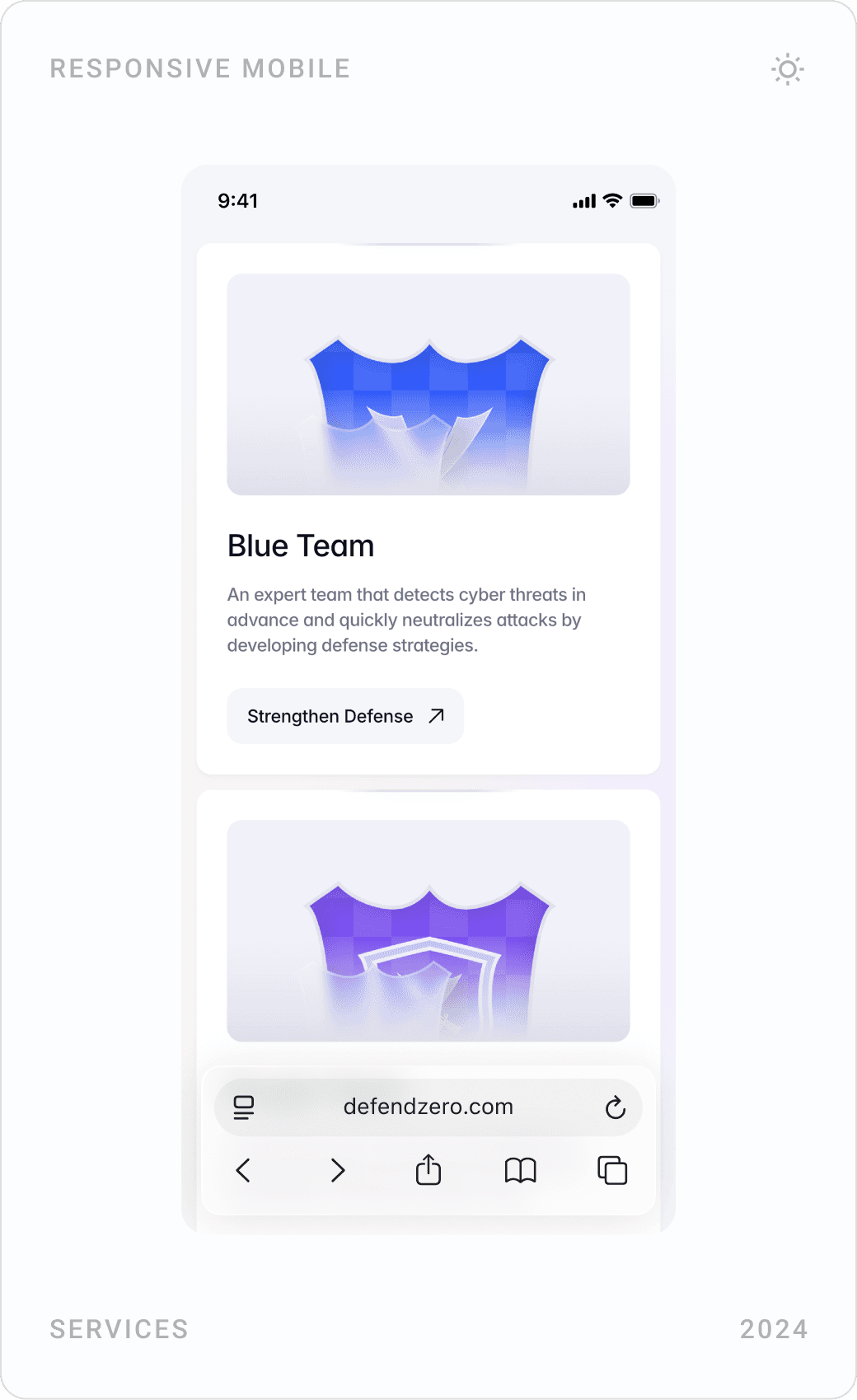
- Structuring complex service offerings like Red Team, Blue Team, and Purple Team operations into a clear, navigable user journey.
- Balancing tech-heavy content (like CVE databases, source code analysis) with modern UI clarity.
- Designing scalable components for ongoing content such as blog posts, FAQs, and vulnerabilities.
100% SUCCESS RATE
We provide strong, innovative, and comprehensive cyber security solutions to protect your digital assets.
Contact Us
PROJECT OBJECTIVES
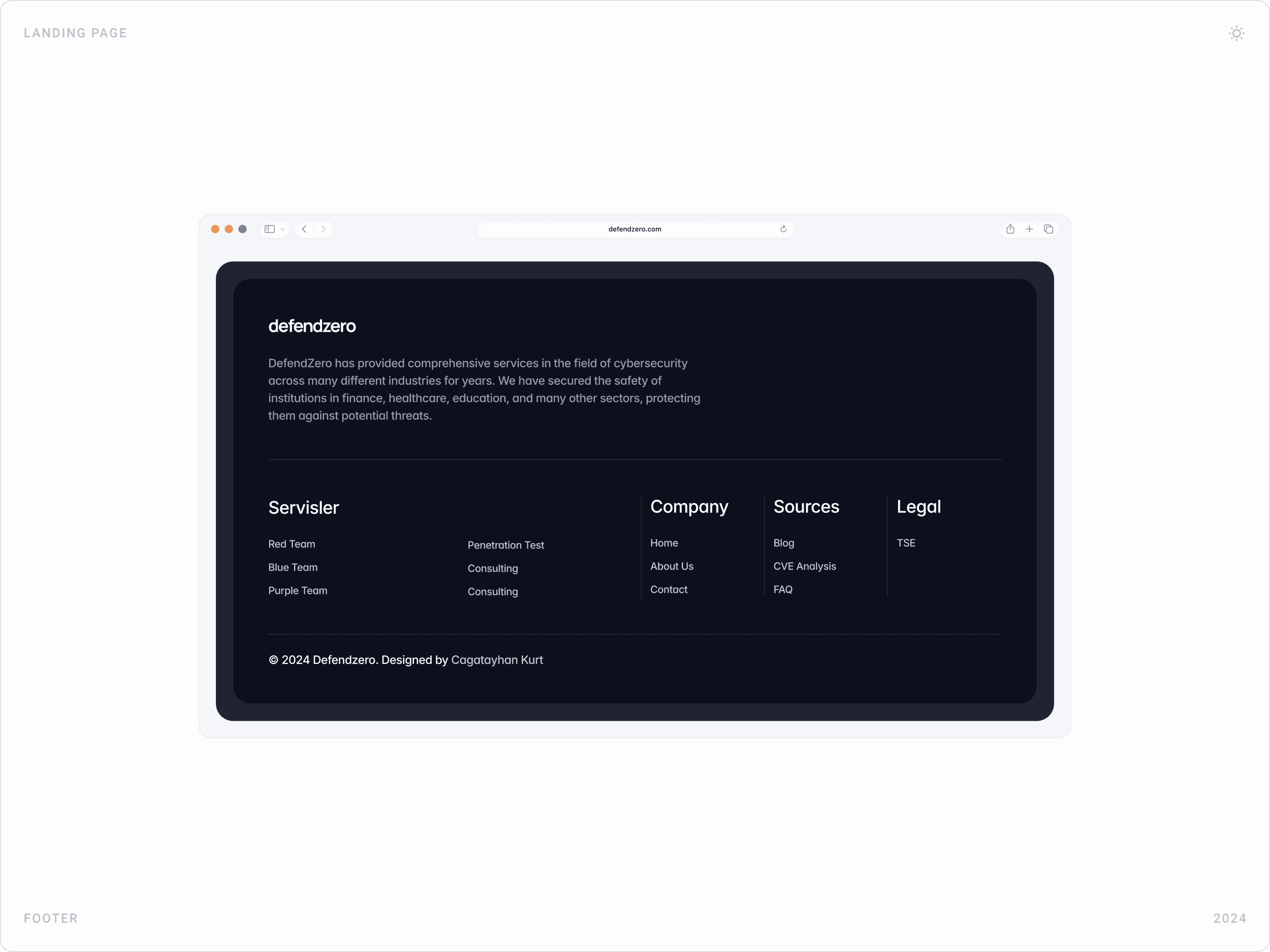
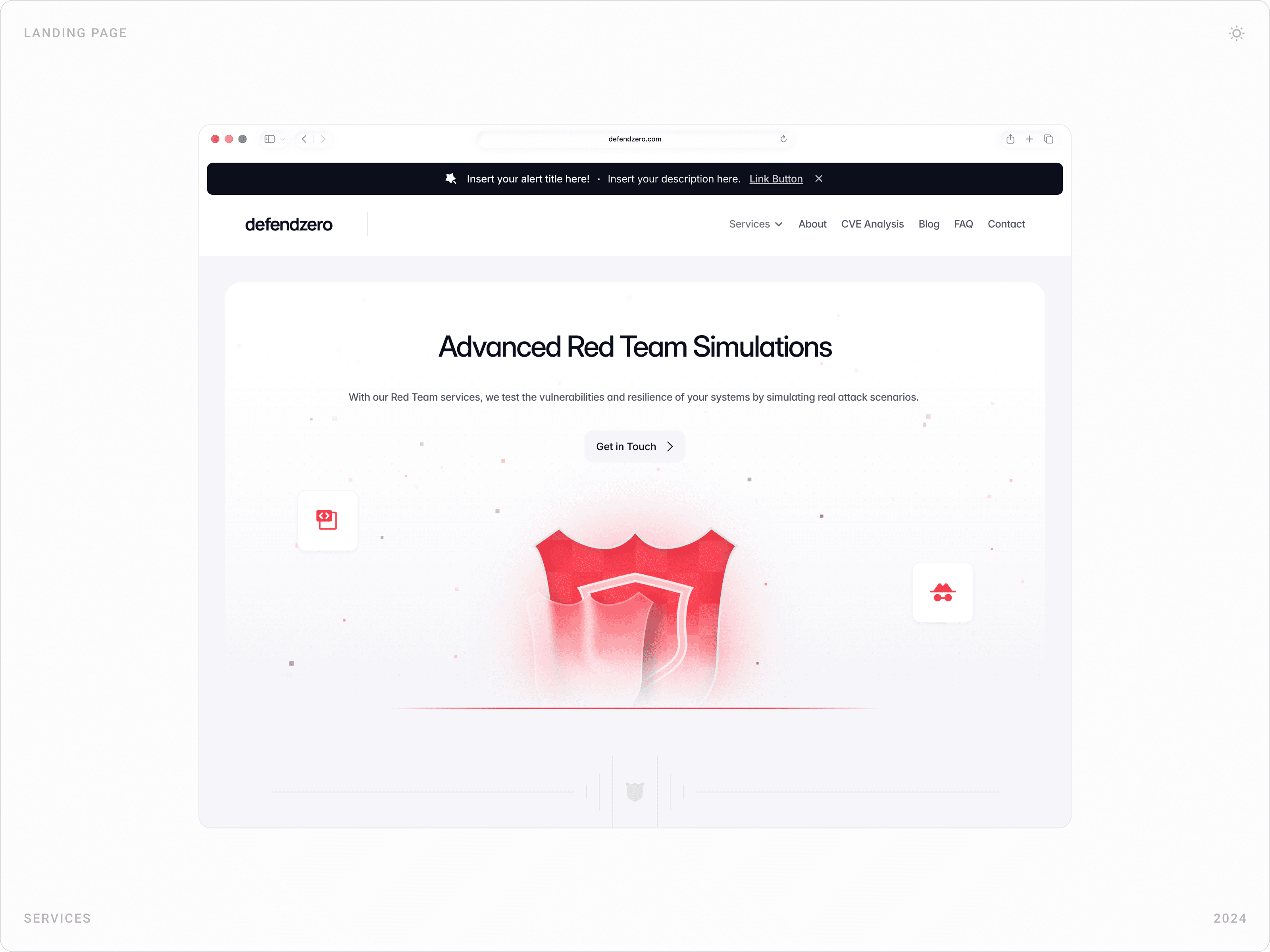
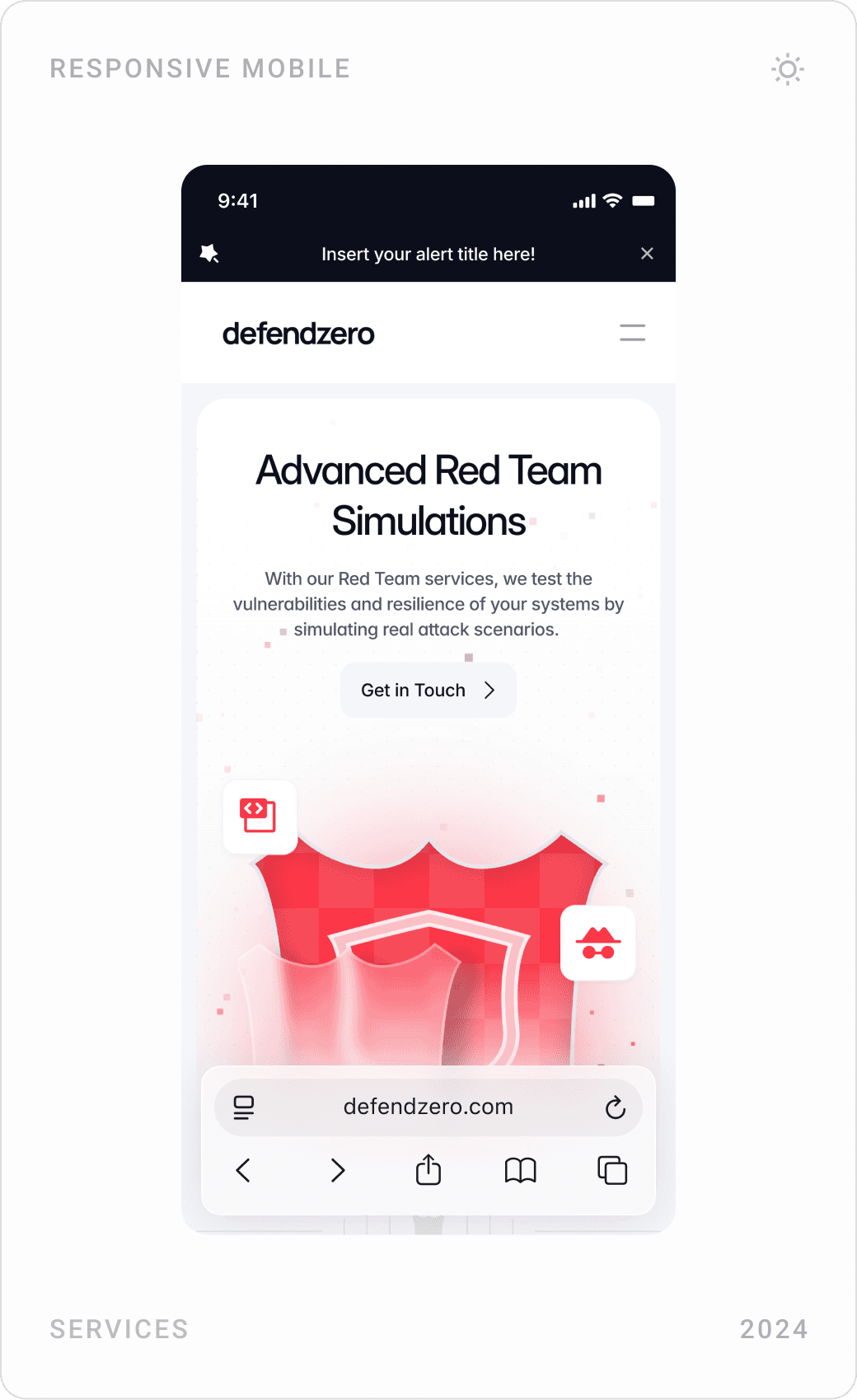
- Design and develop a modern, secure, and responsive website for Defendzero.
- Enable potential clients to understand and inquire about services with ease.
- Showcase Defendzero’s credibility and experience with metrics (e.g., 15+ years, 400+ operations).
- Optimize the platform for SEO and conversion without sacrificing professional tone.


PROCESS & SOLUTIONS
- Research & Wireframing: Competitor benchmarking in the cybersecurity domain helped define clear user flows and CTA placement.
- UI/UX Design: Clean layout, dark/light themes, shield iconography for service areas (Red, Blue, Purple Teams), and security badges for credibility.
- Content Hierarchy: Designed FAQ, contact, service detail, and vulnerability analysis pages with a focus on scannability and quick interaction.
- Development: Built on Framer for a performant, modular, and responsive site architecture with smooth micro-interactions.
- Scalability: Each section (blog, CVE analysis, services) was built with CMS-ready components for easy client updates.
Red Team
An attacker perspective simulation that detects system vulnerabilities with real attack scenarios and strengthens your defense.
Penetration Test
Comprehensive security assessment that reveals your vulnerabilities by testing your systems against malicious attacks.
Consulting
Guidance that maximizes the security infrastructure of your business by providing tailored solutions for your cyber security needs.









GOALS
- Create an authoritative platform for Defendzero that clients trust at first glance.
- Educate visitors on the difference between Red, Blue, and Purple Teams through interactive visuals.
- Provide a direct inquiry system for custom service needs (via form/contact modules).
- Build a foundation for future expansion: threat reports, webinars, whitepapers, etc.





RESULT
110% Increase in form submissions within the first 2 weeks of soft launch.
Mobile performance score of 92+ on Lighthouse.
Positive feedback from cybersecurity professionals on clarity and content structure.
Successfully handed off to client with full CMS control in Framer.